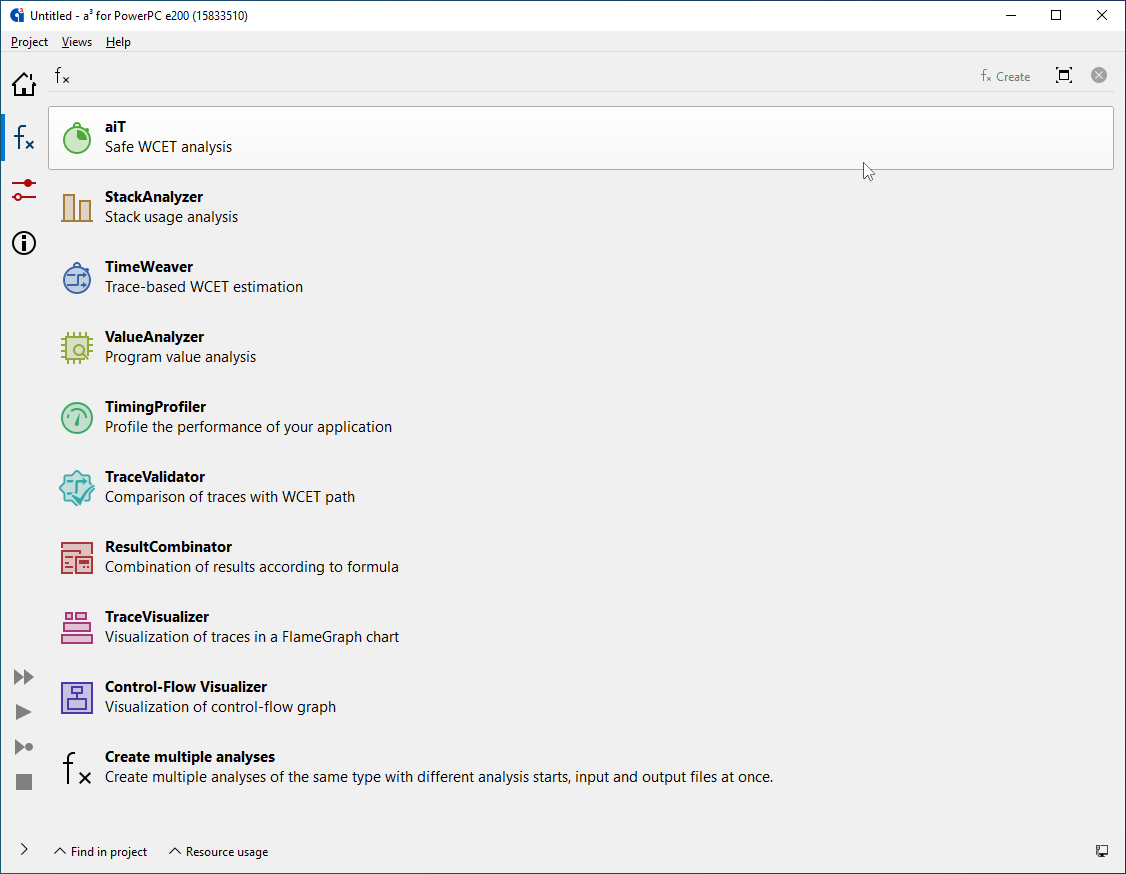
aiT can be combined with other analyzers from AbsInt in a single intuitive user interface.
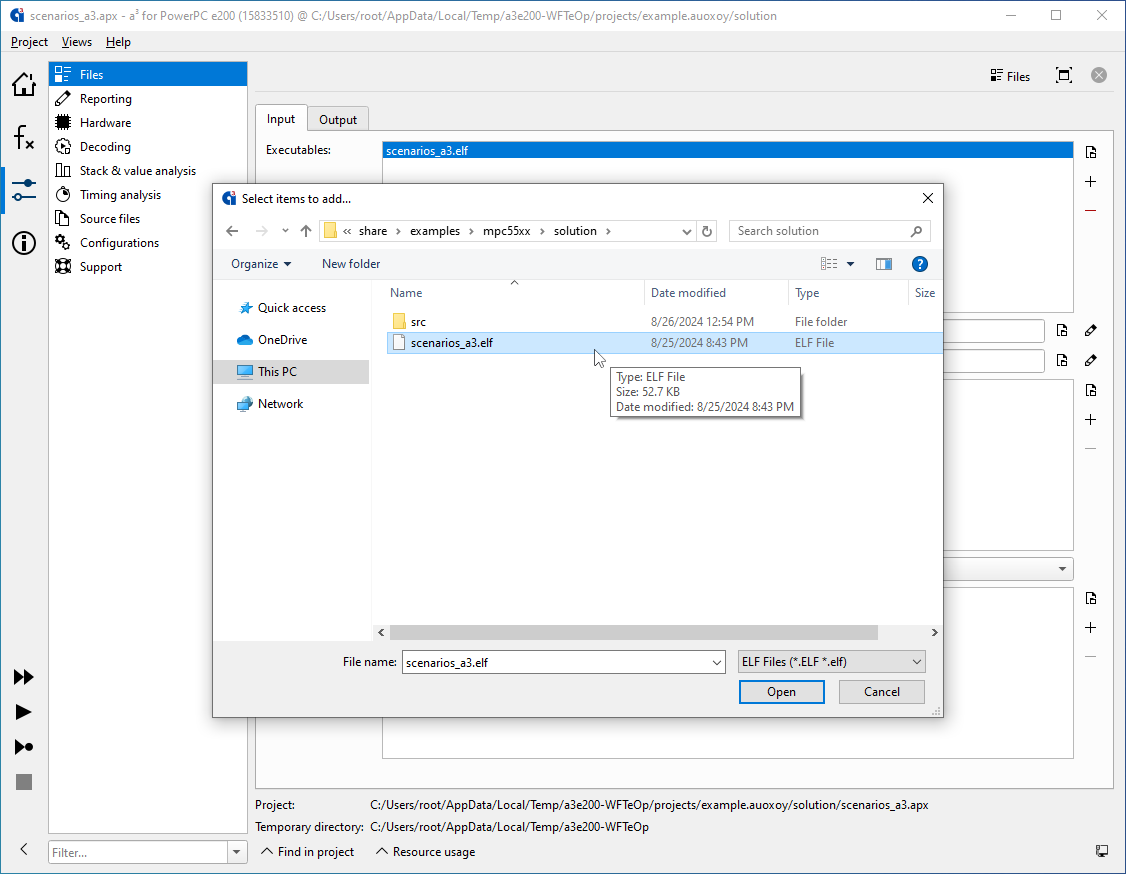
aiT directly analyzes binary executables, so that no modification of your toolchain or the system’s operational behavior or performance is required.
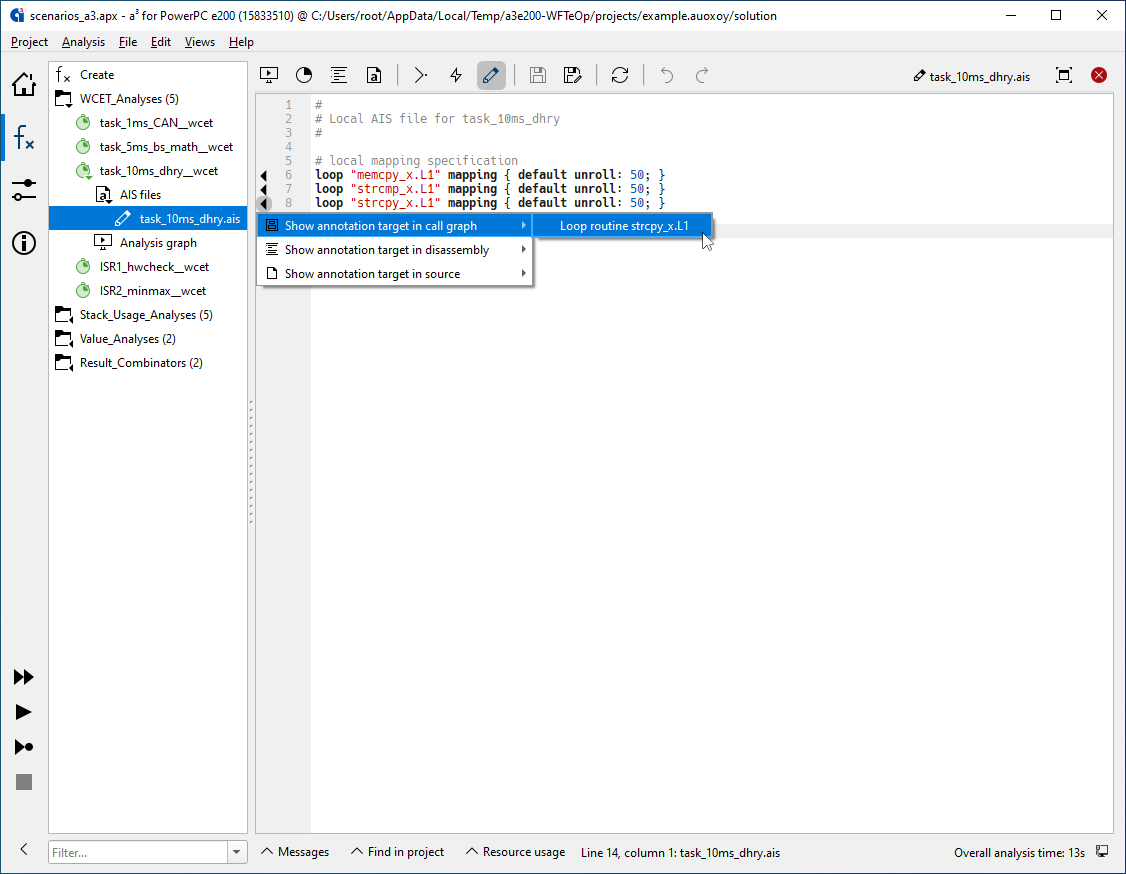
aiT accepts optional user annotations for the analyzed files, such as targets of indirect function calls, upper bounds for loop iteration counts, recursion depth, code snippets that should not be analyzed, infeasible code, and so on.
Annotations are only required if the information cannot be detected automatically by aiT, e.g. for dynamic program properties. The number of required annotations is dramatically reduced using various advanced techniques such as automatic loop-bound and array-call recognition.
Annotations can be provided in a separate text file, or by using the fully integrated annotation wizard that will generate such a file automatically based on your input.
“aiT is very easy and straightforward to use. While it does provide a lot of configuration options, one can get to a first WCET computation result very quickly. Advanced configuration through annotations can be added later. [… It also] has by a wide margin the best capabilities to resolve dynamic calls automatically.”Independent study by the University of Stuttgart (PDF)
“aiT is able to find better loop bounds[, resulting in] fewer data cache misses”
TU Vienna (PDF)
“aiT was pretty straightforward to use and did not cause any major problems that could not be dealt with quickly; in particular, it could deal with almost all branches without further interaction”
WCET Tool Challenge 2011 final report (PDF)
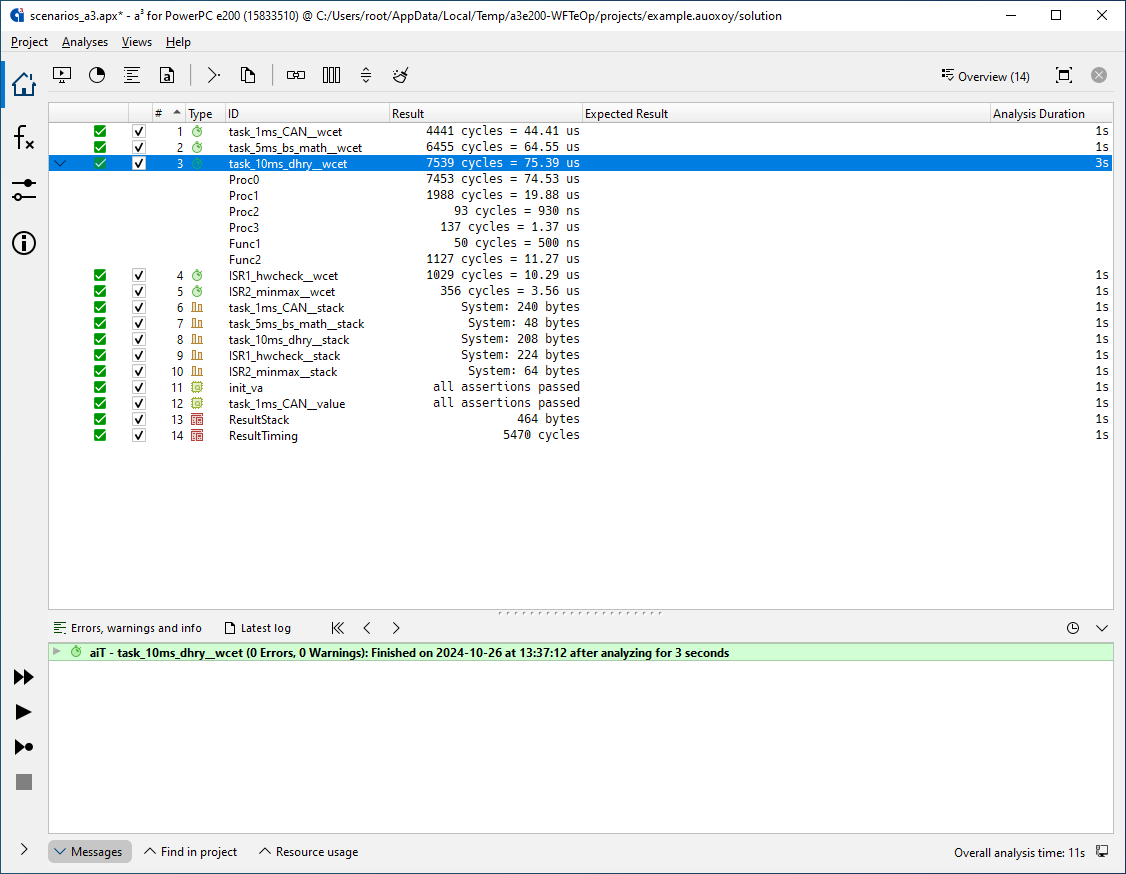
Analysis results: the computed WCET is given in CPU cycles and microseconds. aiT-computed bounds are valid for all inputs and execution scenarios.
Double-clicking on the analysis results opens the call graph of the analyzed application.
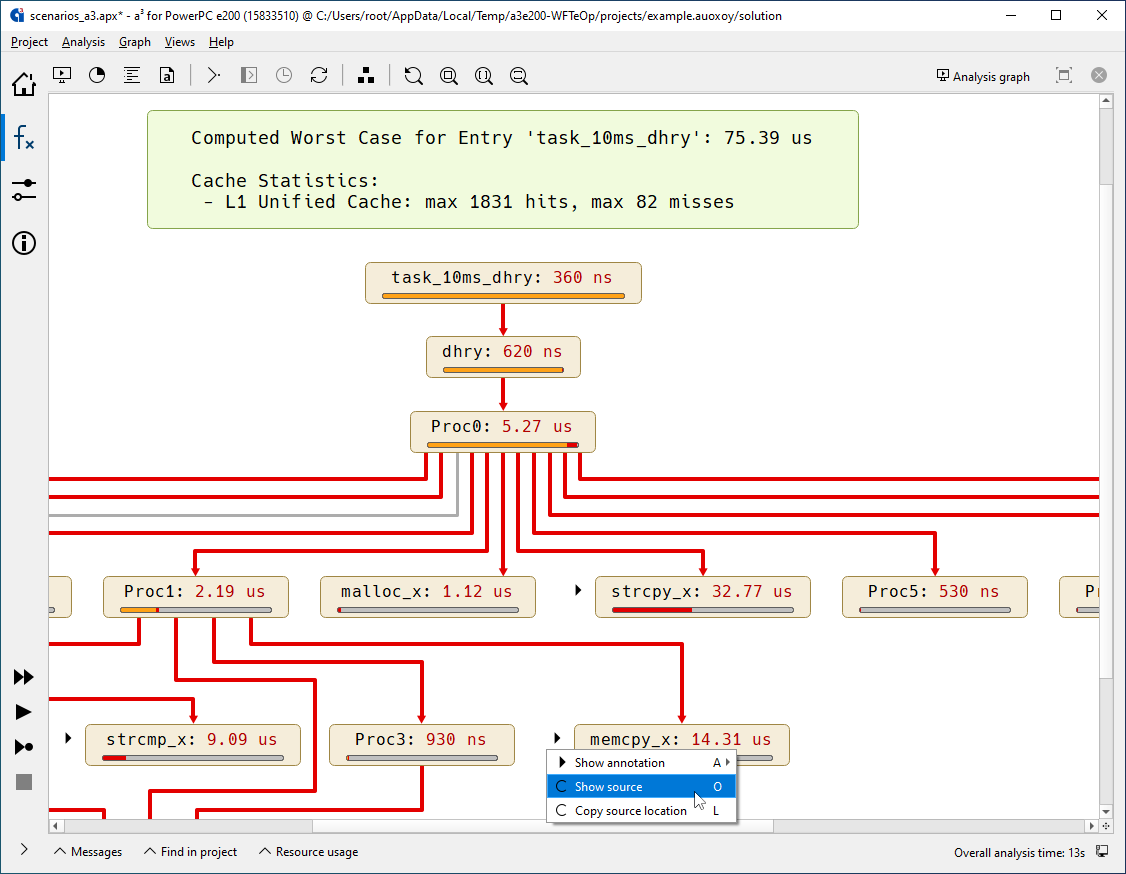
Call graph with WCET analysis results. Each routine is annotated by its relative contribution to the overall WCET. Worst-case execution paths, infeasible calls, and recursions are automatically recognized and highlighted.
aiT also automatically determines any locations that could benefit from additional annotations, marks them for you, and even suggests the best wording for the annotation that you can then accept or modify with a couple clicks.
The routines can be interactively unfolded to inspect the control flow within them.
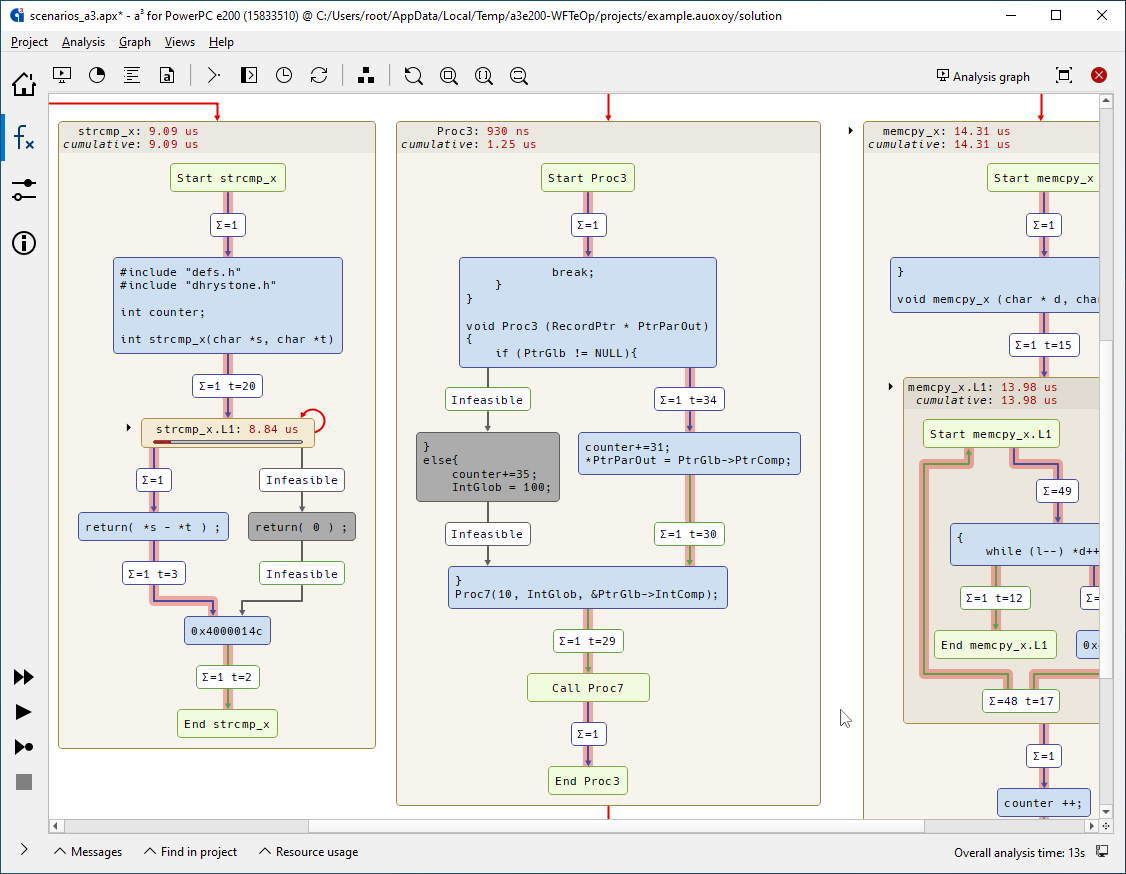
Control flow graph with WCET analysis results. Each edge is labeled with the maximum number of traversals in the worst case and the execution time of the basic block it originates from. Infeasible parts of the analyzed program (dead code) are grayed out.
Analysis details such as WCET contribution in different contexts can be inspected with ease. Context menus enable jumping from anywhere in the graph to the corresponding line in the source or assembly code.
Just like at the call-graph level, any locations that could benefit from additional annotations are automatically marked, and the best wording is automatically suggested, so you can fine-tune the analysis with just a few clicks.
Basic blocks can be further unfolded to inspect the instructions within, and for each instruction, the set of all possible pipeline states can be inspected as desired.
“A clear winner in terms of additional functionality is AbsInt, which provides tools like a syntax-aware editor for annotations including a wizard for easily adding annotation lines, and an interactive call-graph viewer. The other tools have static output which may be viewed, but cannot be interacted upon.”Independent study by University of Stuttgart (PDF)
“aiT was pretty straightforward to use and did not cause any major problems that could not be dealt with quickly; in particular, it could deal with almost all branches without further interaction. We checked the resulting call graphs for overestimation of loop bounds — which were mostly automatically computed — but they were all reasonable.”WCET Tool Challenge 2011 final report (PDF)
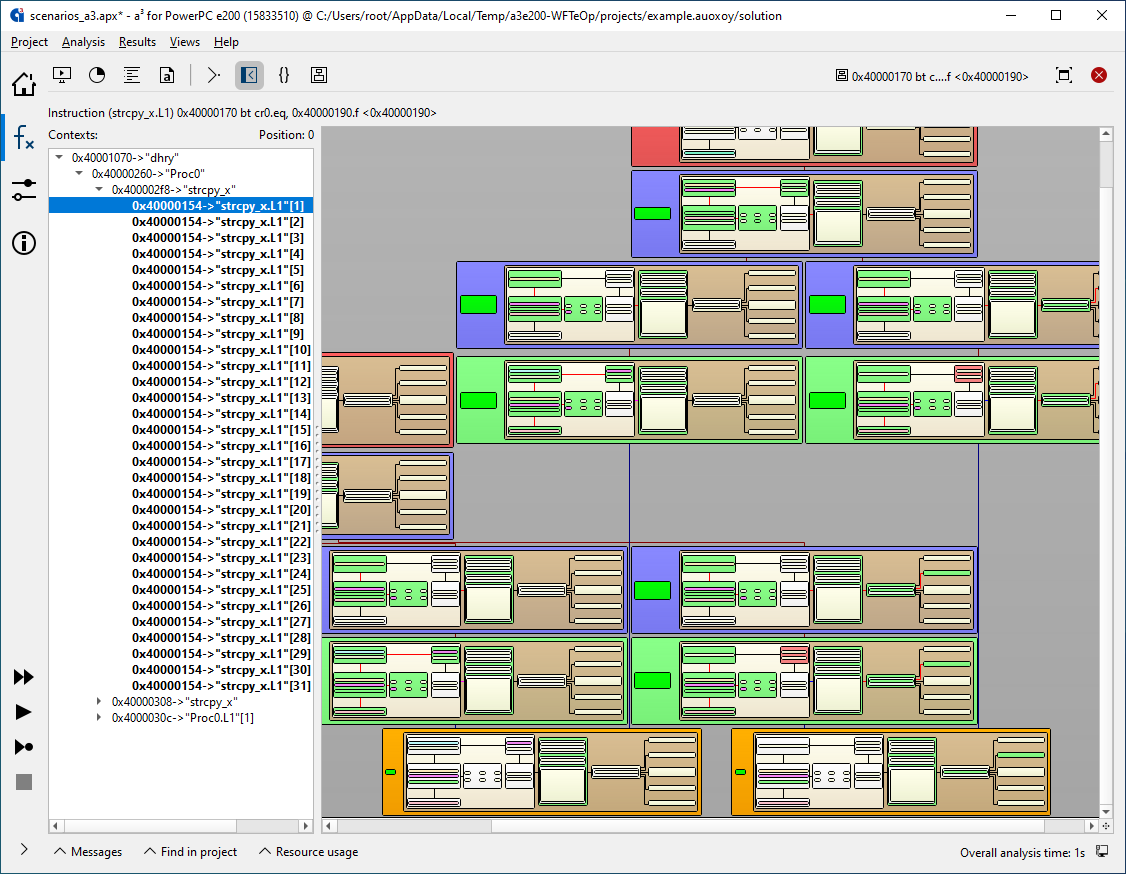
Visualization of pipeline and cache behavior over time. Each horizontal layer corresponds to one CPU cycle. Branches in the tree represent different execution scenarios, e.g. a cache hit and a cache miss at a memory access if both cases have to be analyzed. aiT automatically checks all possibilities.
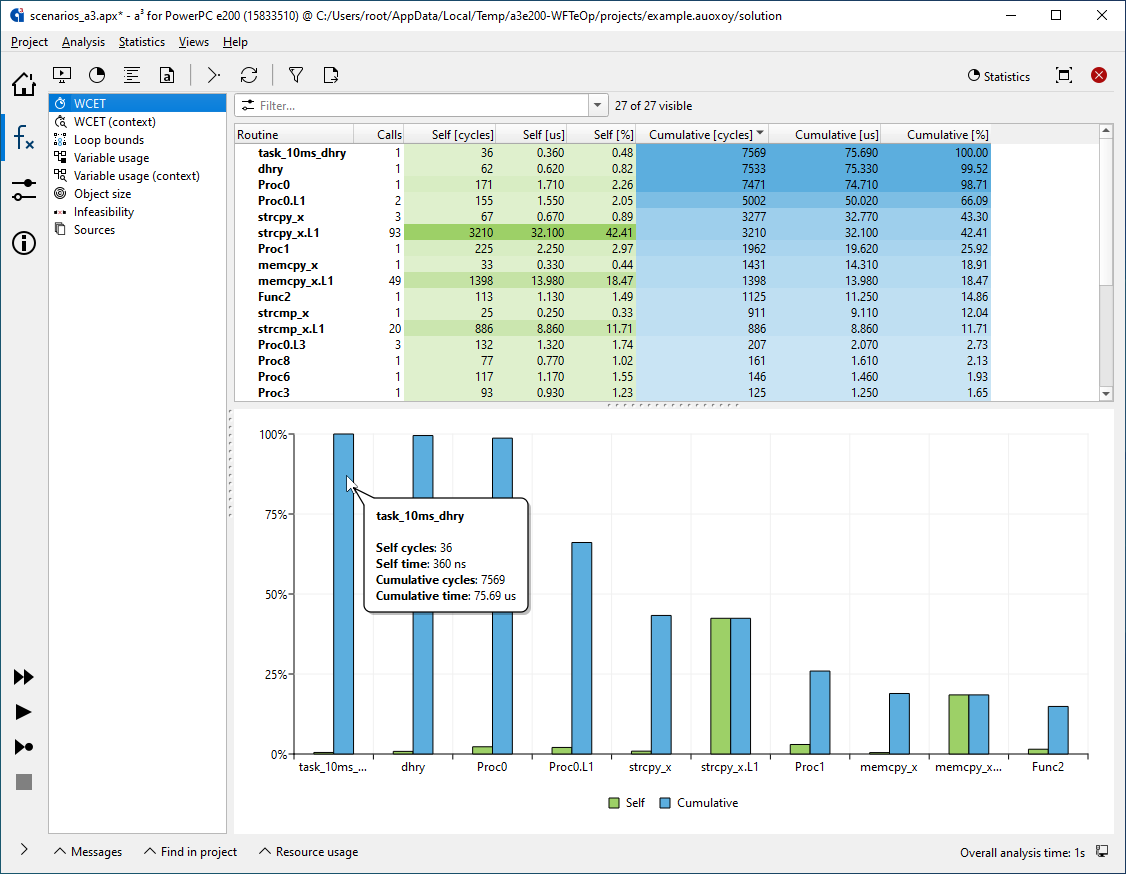
Various statistics are compiled so you can quickly identify bottlenecks and easily explore areas of interest.
Customizable XML reports can be exported for integration, documentation, or certification purposes.
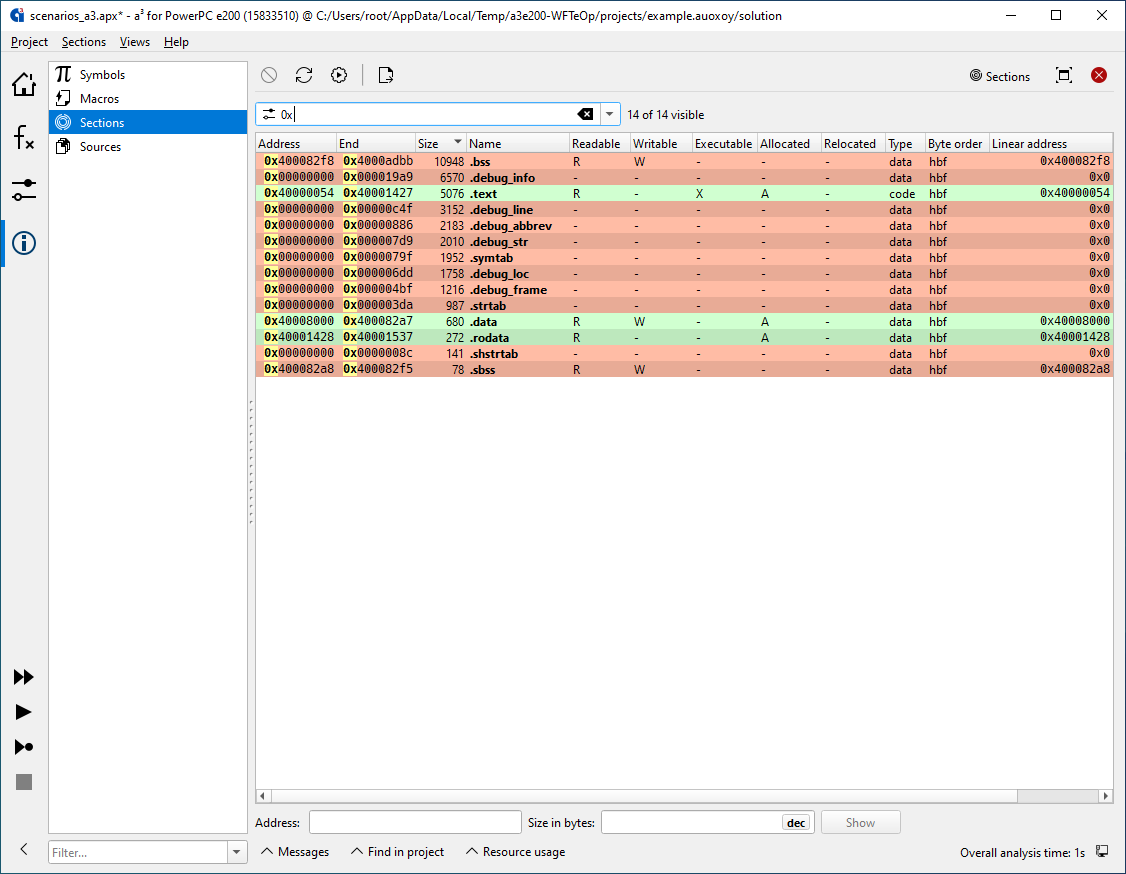
The Sections view allows you to view all sections of the binary and inspect their content like in a hex editor. It also enables you to find out the memory content for a given address area.
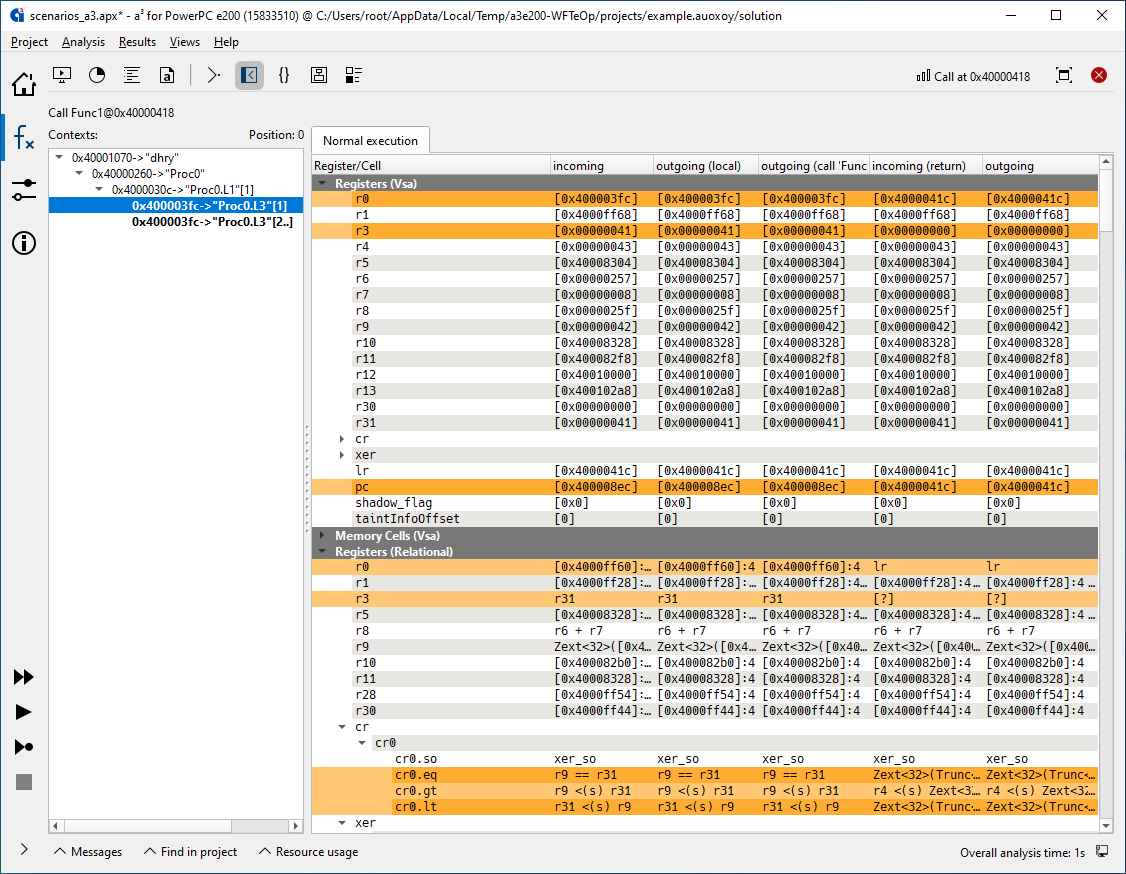
- An optional ValueAnalyzer add-on lets you inspect the contents of all registers and memory cells at any program point in any execution context. It can also collect initialization data for global variables and feed it as auto-generated annotations to your WCET analysis, further reducing the need for manual annotations.
- If you haven’t yet decided on the exact processor derivate for your application to run on — or if the final decision is not yours to make —, you can use TimingProfiler to develop your application in a timing-conscious way from day one. Once the hardware has been decided on, you can then easily switch to aiT, within the same GUI, keeping all your settings and annotations, and without having to install anything.
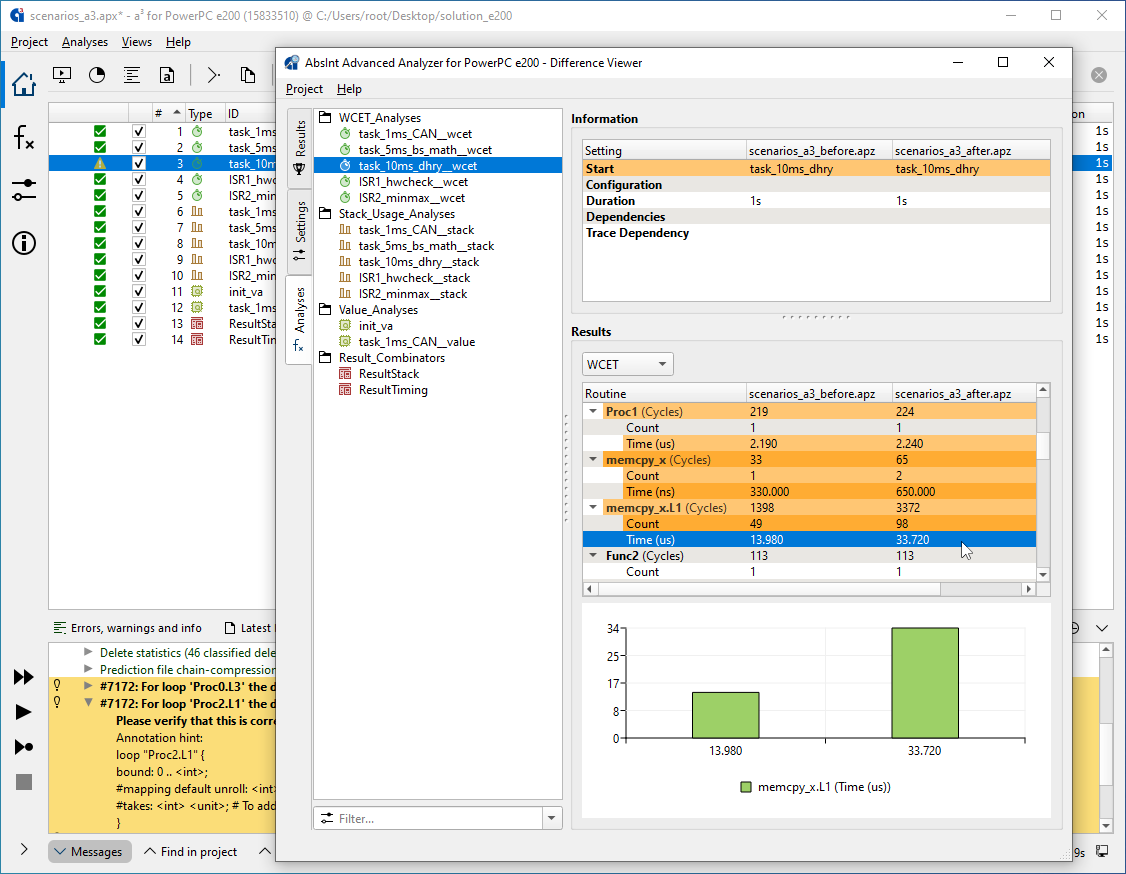
Difference analysis lets you compare analysis runs before and after making changes to your system, such that their effect on the worst-case timing can be understood immediately and completely.
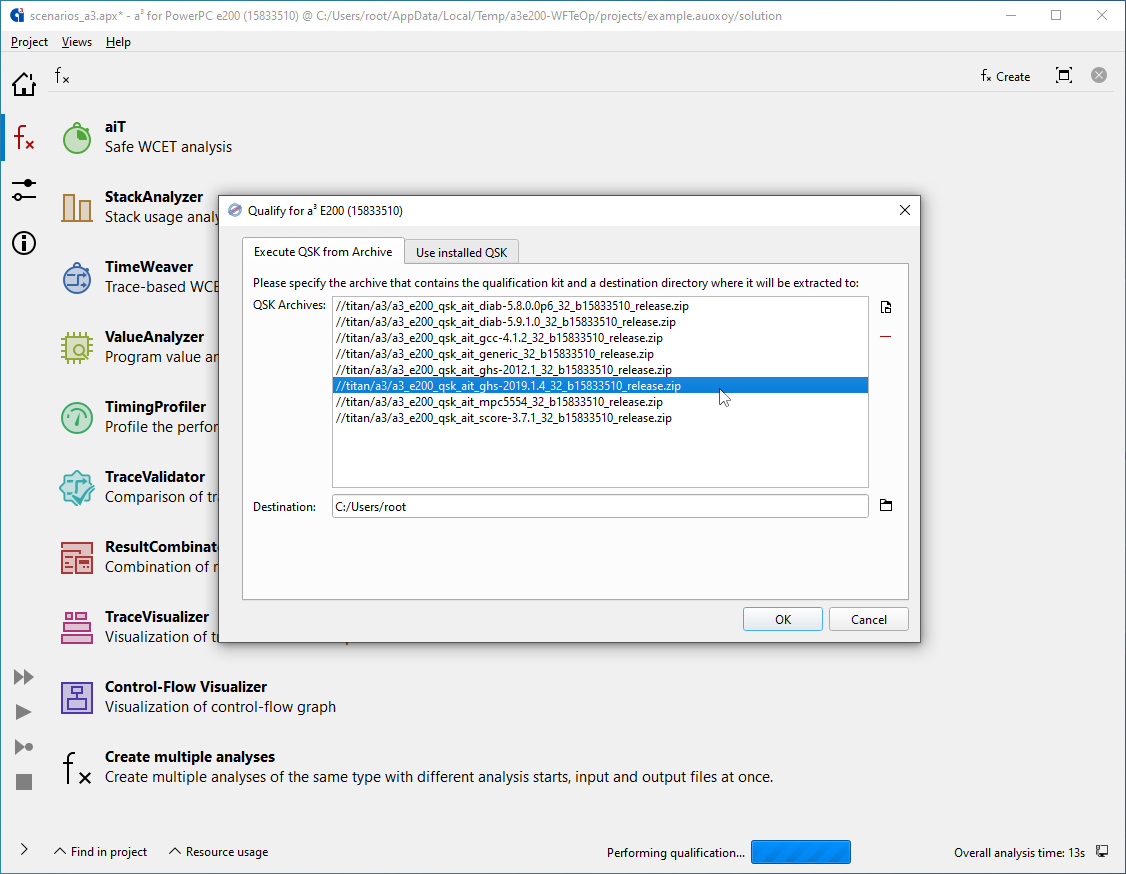
Your usage of aiT can be qualified according to ISO 26262, DO-178B/C, IEC-61508, and other safety standards. Special Qualification Support Kits can be started directly from within aiT to help you simplify and automate your qualification process.