ValueAnalyzer is a tool for static analysis of register and memory contents. It is particularly useful for:
- verifying the absence of illegal accesses to an embedded software system from within third-party modules provided as object code
- initialization analysis for execution-time or stack-usage analyses, to improve precision and minimize manual annotations
Verifying the absence of illegal accesses
When developing complex safety-critical software systems, it is quite common to integrate third-party object code in it. However, it is usually difficult to verify that such code only does what you want it to do:
- it might read variables it must not read
- it might write variables it must not write
- it might call functions it must not call
Common reasons for such illegal accesses to your system by third-party code are:
- programming errors (e.g., an iterator exceeds an array limit)
- non-compliance with specifications
- compiler or linker errors
Illegal accesses may cause problems in the field. Additionally, license or liability issues can arise.
ValueAnalyzer provides the solution to these problems. It statically analyzes object code and reports any violation of your spec.
Initialization analysis
A common principle in embedded control software is that global data structures like (function-)pointer variables are initialized in separate code sections. Consequently, when a task or runnable is analyzed for its worst-case timing or stack usage, these initializations are unknown. This usually leads to a less precise analysis with more manual annotations.
With ValueAnalyzer you can automatically collect initialization data for global variables and feed it as auto-generated annotations to a WCET, stack-usage, or yet another value analysis.
Dead code elimination
Modern development standards such as DO-178B require unreachable code to be eliminated. Since the required testing effort is high, it is desirable to remove unreachable code as early as possible.
ValueAnalyzer automatically identifies code that is provably unreachable during any program execution.
Features
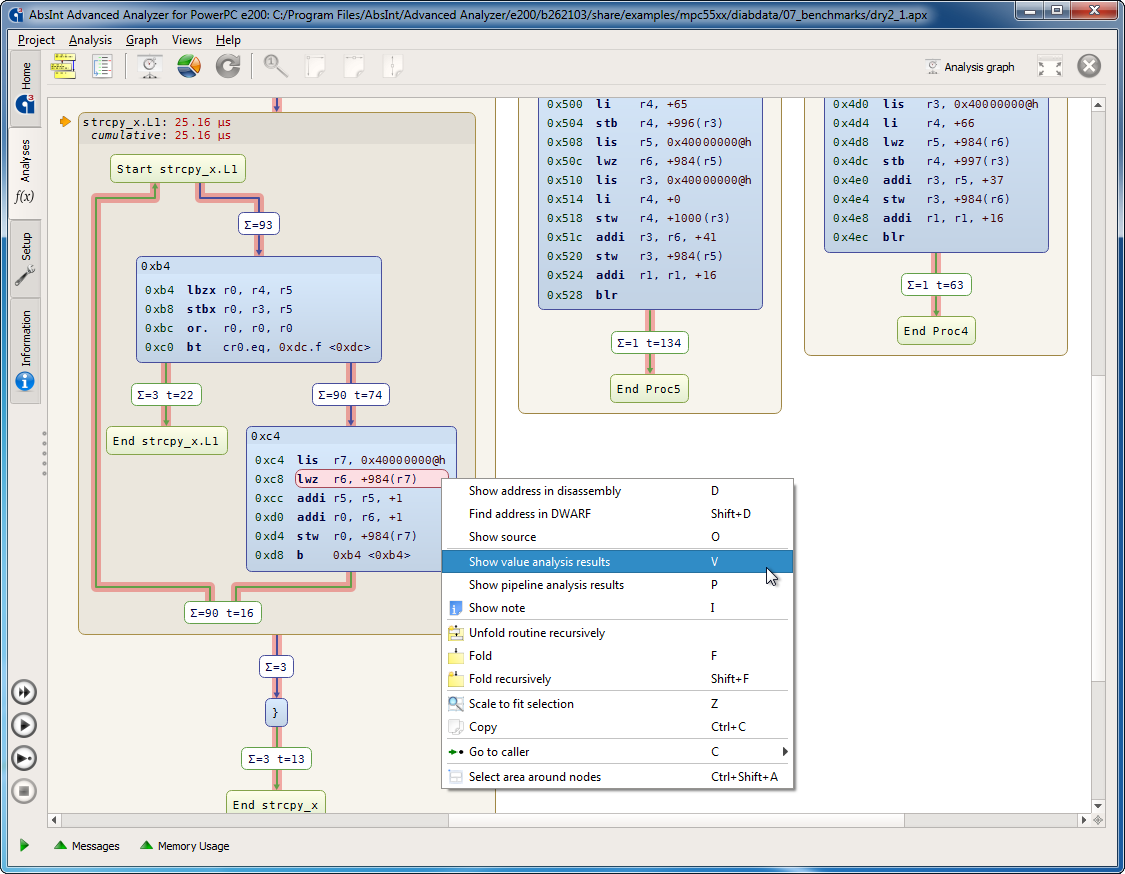
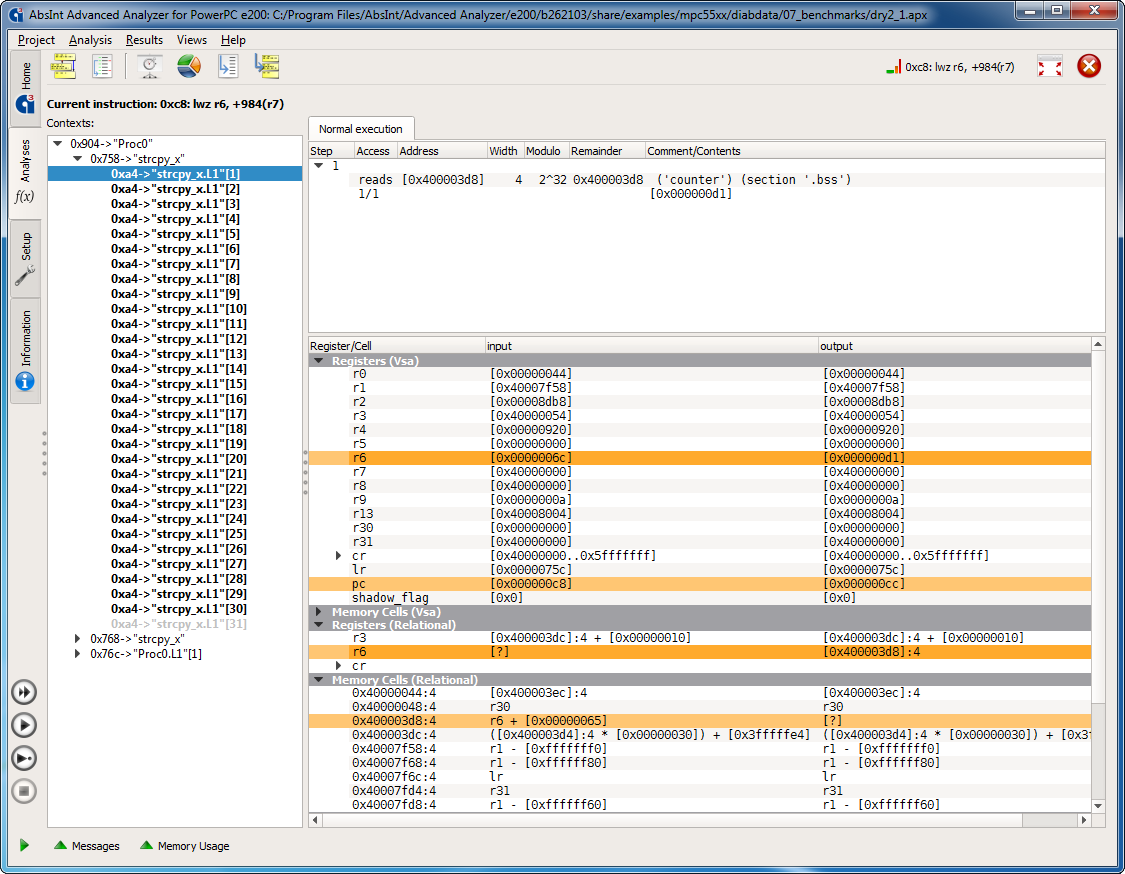
- Interactive, easily explorable analysis results. Contents of registers and memory cells are shown before and after instruction execution per context.
- Comprehensive reports on:
- all memory accesses per function
- all calls to user-selected functions
- all accesses to user-selected memory areas
- register and memory contents at the entry/exit of selected functions
- Validation of static user-defined assertions, such as:
- assertions that a user-selected instruction or function does (not) access a user-selected memory area
- global assertions on user-selected memory areas (is read-only, is write-only, is inaccessible…)
- Detection of unreachable code. Code reported as unreachable is guaranteed to be unreachable for all possible inputs and each program execution under any circumstances.
- Seamless integration with StackAnalyzer, aiT WCET Analyzer, TimingProfiler, and/or TimeWeaver in a single intuitive user interface.


- Plugin for Jenkins, the leading open-source automation server.
Your benefits
- The analysis is fully automatic and valid for all inputs. No input patterns need to be provided.
- The analysis is conservative, i.e. the results are safe. All illegal accesses that are present will also be reported.
- Supplied third-party software can be analyzed right away. It does not have to be integrated on the ECU.
- No debug information is required. The results are not affected by possible bugs in the debug output.
Supported processors and compilers
ValueAnalyzer is available as an add-on to aiT, StackAnalyzer, TimingProfiler, and TimeWeaver, for all processor–compiler combinations supported by these tools.
Free trial
Start your free trial today, complete with free online training and technical support.